CUDR, Data Layer Born for Network Slice
Time:2019-03-07
5G is coming. Compared with 4G, 5G is a disruptive technology renovation, and it will be the foundation for the digital transformation of the whole society. In the 5G era, single physical network cannot meet SLA (Service-Level Agreement) requirements of various vertical industries. In this case, 5G network slicing technology is generated to address individualized and differentiated service demands. Operators can divide the network into multiple slices, and each slice is a complete logic network provided for different users. Slices are completely isolated, causing no impact to each other.
As shown below, network slicing flexibly allocates network resources and combines network capabilities. On the basis of one 5G network, it virtualizes multiple logic sub-networks with different features, to provides on-demand customized network service for different scenarios.
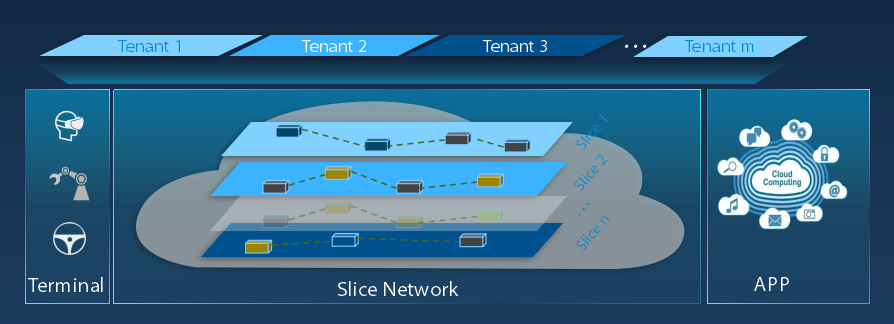
Figure 1 Architecture of Network Slicing
Facing the new changes, the architecture of 5G Core needs innovative transformation to support network slicing and meed diverse demands of the 5G network.
With Service Based Architecture (SBA) being introduced to 5G Core to facilitate the integration with vertical industries, service-based interfaces replace traditional point-to-point interfaces, and control and user plane separation (CUPS) is achieved. In addition, in the 5G Core, data management function is independent. It uses independent data layer to separate applications from data, and it uses stateless design to achieve rapid scaling and high reliability.
To achieve unified data layer, 3GPP defines two Network Functions (NF), Unified Data Repository (UDR) and Unstructured Data Storage Function (UDSF). UDR stores users’ profiles, static subscription strategy data, and data of Network Exposure Function (NEF). UDSF stores user session, state, link and other information generated by each NF in the 5G Core, to be used by specific NF or NF group.
To meet diversified demands of 5G networks, network slicing needs a unified data layer to provide differentiated services. To address this requirement, ZTE promotes the Cloud Unified Data Repository (CUDR) solution.
ZTE CUDR Solution
ZTE CUDR solution aims to provide agile information infrastructure for next-gen telecom cloud through cost-effective hardware and efficient automatic creation. This solution is based on the advanced Universal Subscriber Profile Platform (USPP) architecture, learns the experience of serving about 200 global operators, and uses the microservice design concept, meeting 3GPP’s requirements on data service, to build a 5G-oriented, cloud-based, converged open data layer.
ZTE CUDR solution supports UDR and UDSF defined by 3GPP, and is also fully compatible with the User Data Convergence (UDC) function of 2G/3G/4G networks, flexibly meeting operators’ different deployment demands. In the 4G era, ZTE’s UDC product leverages advanced distributed architecture, supports atomic application convergence, multilevel protection and layered storage technologies, and is combined with virtualization cloudification technology, which makes it leading the industry. Now, ZTE CUDR product adopts advanced service-based design concept, and supports unified data and unstructured data engines, to carry out flexible service orchestration and deployment and provide reliable security mechanism, so it fully fits network slicing scenarios. Therefore, it will help operators achieve network transformation to build more intelligent, flexible, highly-reliable telecom network.
Highlights of ZTE CUDR solution: flexible deployment modes, high reliability and security, high performance, ultra-large capacity, rich data analysis and mining, and intelligent operation and maintenance (O&M). In terms of flexible deployment modes and data security, this solution is closely related with network slicing.
- CUDR achieves flexible deployment
On the one hand, in CUDR, unified data and unstructured data engines use two different data engines services which can be flexibly deployed on demand. CUDR can serve one or more NFs at the same time; it can serve multiple NFs (UDR or UDSF) of the same type or different types (UDR + UDSF). On the other hand, based on the distributed architecture, CUDR’s network orchestration center is able to flexibly deploy CURD instance nodes according to different network slicing scenarios. CUDR can be deployed in a centralized manner or close to NF to address URLLC scenarios. For example, deploying CUDR instance in the center node to carry out centralized management for large-capacity user data, or deploying CUDR instance at the access node to perform rapid data read and write in collaboration with other NFs, reducing network latency and improving user experience.
- CUDR achieves security isolation of slices
To address the security isolation requirement of slices, CURD performs data isolation through DB multi-instance or multi-tenant mechanism.
On the one hand, CUDR can create multiple DB instances distributed on different nodes and serving different network slices. On the other hand, CUDR can work as public NF to serve multiple slices. Under one DB instance, CUDR can create multiple tenants. Each tenant has different rights, and its logic resource is isolated from other tenants. Different network slices or different NFs in one slice can use different tenants to organize and access data. CUDR can achieve: data storage isolation and data access isolation; operation and maintenance isolation, so that data upgrade does not impact each other; independent lifecycle management, so that scaling does not impact each other. In addition, according to data type and service requirements, CURD automatically plans and deploys node distribution, capacity information, and load balance of data instances, to guarantee data isolation, reliability and integrity.
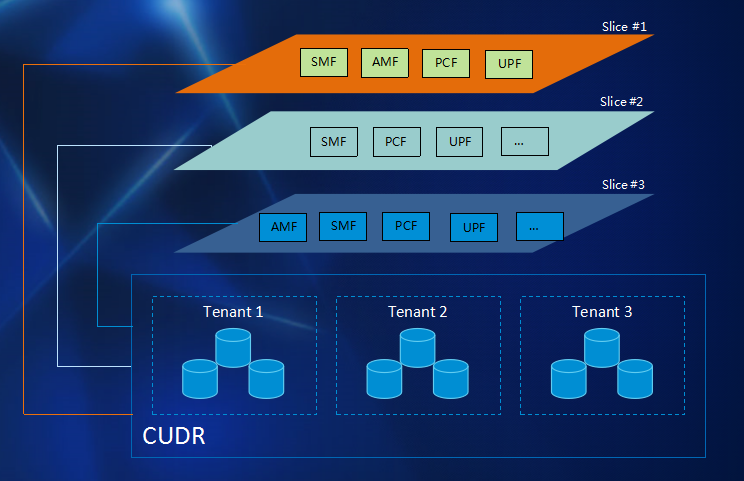
Figure 2 Architecture of CUDR
ZTE 5G-oriented CUDR solution builds independent data layer for network slicing, addressing diversified application requirements of vertical industries, and facilitating operators performing network renovation.

